Azure AD Password Protection significantly lowers the risk of a “password-spray attack”, which uses common passwords that are usually selected by user groups within an organization to get access to corporate resources.
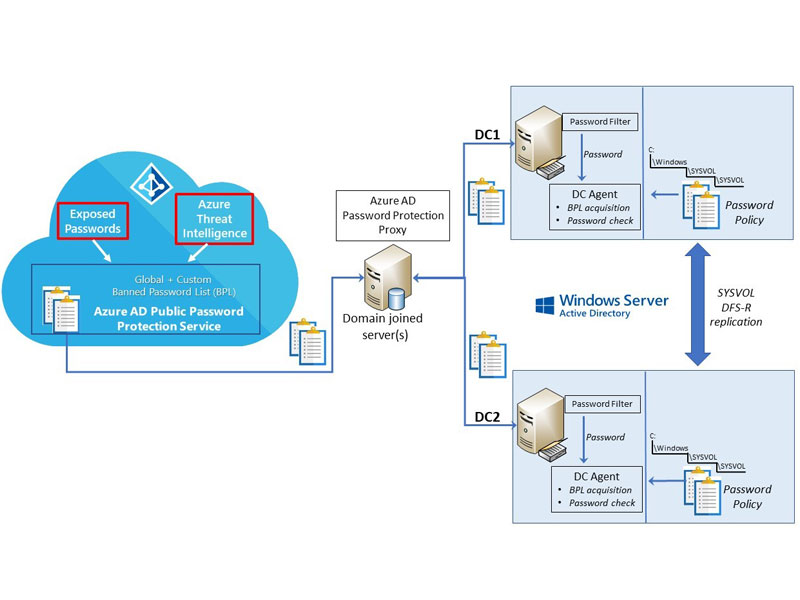
IT administrators can use this solution to customize lockout settings for both their cloud and hybrid environments. It works with a banned password algorithm, which doesn’t allow the use of easy-to-guess passwords. Microsoft has a list of passwords cataloged as vulnerable and that, therefore, can’t be entered by users. In addition, each organization can add whatever they consider appropriate for their particular case, such as, for example, the name of the company itself or the surnames of the workers.
Administrators of an application and desktop virtualization platform in the cloud with UDS Enterprise and Azure will be able to take advantage of this new feature, since this connection broker supports Azure AD, allowing to directly validate users or groups of users registered in this authenticator.







0 Comments